../PID spoofing
22 August 2025
What is Parent Process ID (PPID) Spoofing?
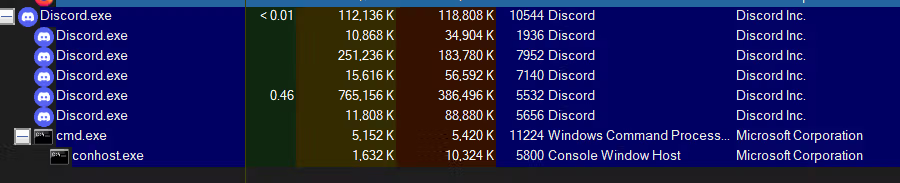
EDR (Endpoint Detection and Response) systems often track parent-child relationships between processes on Windows. For example, If Microsoft Word (winword.exe) spawns rundll32.exe, the EDR may flag this as suspicious because Word normally doesn’t create that child process. Attackers can try to hide malicious activity by faking or spoofing the parent process of their malicious process.
What is the Goal?
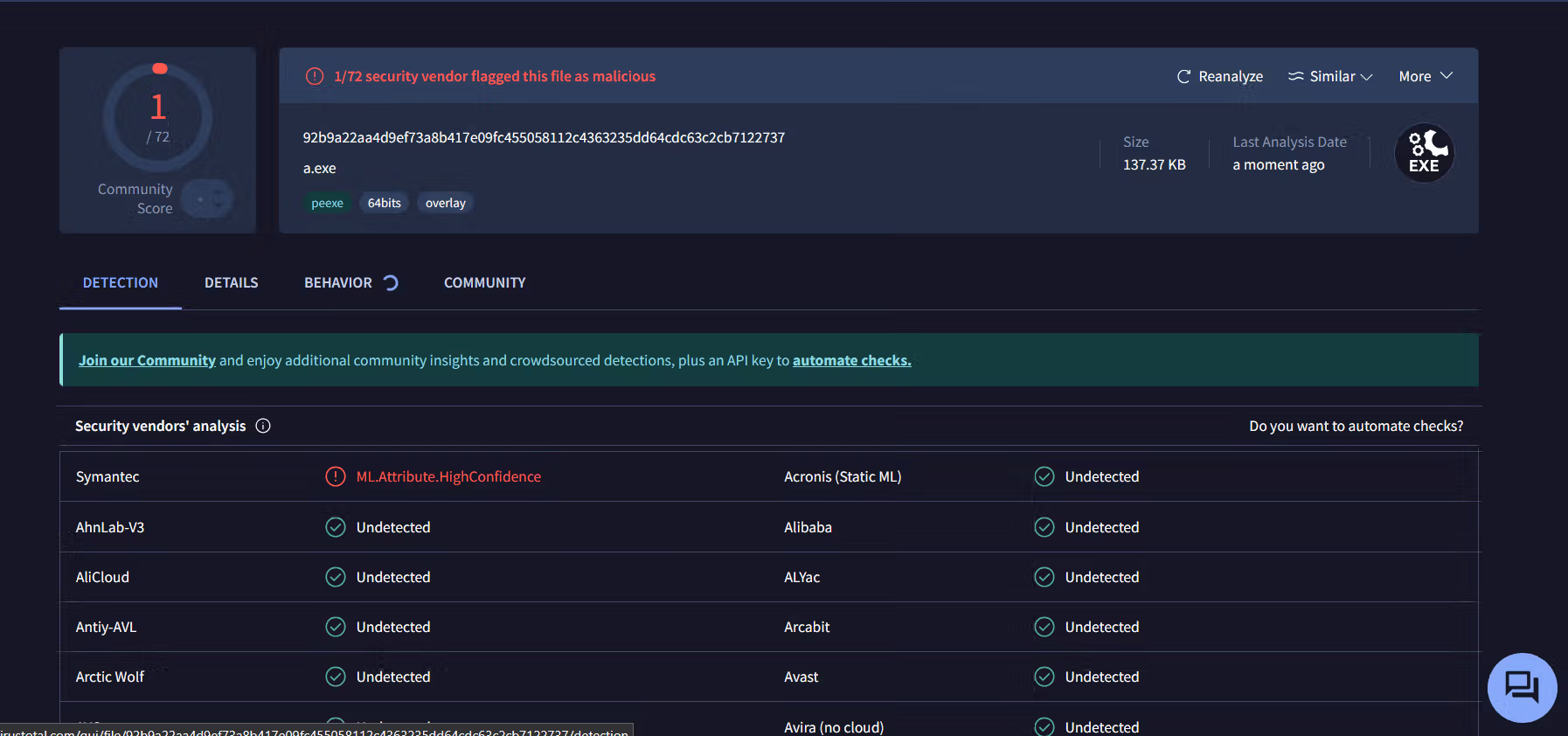
The main goal of an attacker performing PPID spoofing is to evade detection by security tools. By masking the true parent process, the malicious process blends in with legitimate activity, avoids alerts from EDR systems, and can execute payloads stealthily without raising suspicion.
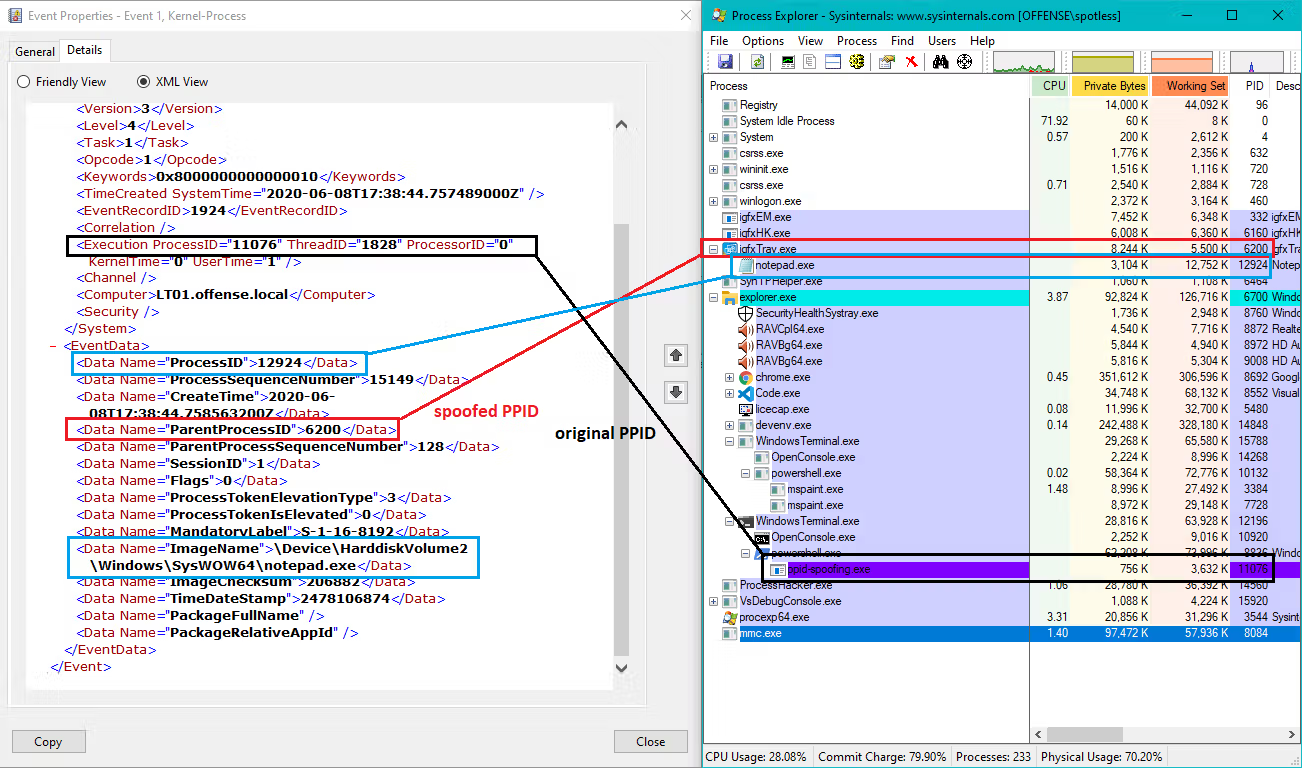
How spoofing Works?
The primary technique involves manipulating the child process’s attributes during creation, specifically using the CreateProcess API in Windows.This API allows specifying a parent process ID (PPID) through the PROC_THREAD_ATTRIBUTE_PARENT_PROCESS attribute.By setting this attribute, an attacker can assign a malicious process to appear as a child of a trusted parent process, such as explorer.exe.This manipulation enables the malicious process to inherit attributes like the current working directory and environment variables from the spoofed parent, potentially evading detection mechanisms that monitor parent-child process relationships.This technique was popularized by Didier Stevens in 2009, who demonstrated its effectiveness in bypassing security tools that rely on process lineage for detection.