../Unhooking NTDLL
22 August 2025
Why Unhook?
Modern Endpoint Detection and Response (EDR) solutions often rely on inline hooking within user-mode DLLs, mainly ntdll.dll, to detect and block suspicious or malicious activity. These hooks let EDRs intercept sensitive system calls like NtOpenProcess, NtCreateThreadEx, and NtAllocateVirtualMemory.
How Hooks Work
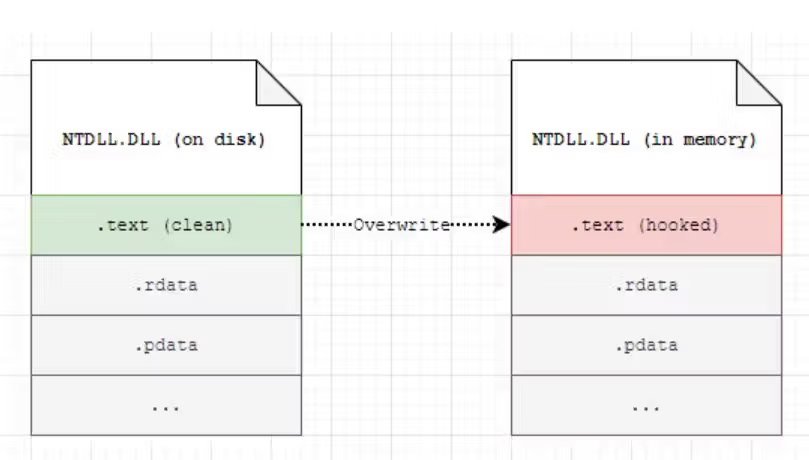
When a process starts, the system loads ntdll.dll into its memory. EDRs often modify specific instructions in the .text section of this DLL. For example, instead of letting the original syscall instruction run directly, an EDR may replace the function prologue with a jump or call to its own monitoring routines. This redirection enables them to log, block, or alter the behavior of the call.
Why This Is a Problem
For red teamers, malware authors, or even developers who need clean access to system calls, these hooks create barriers. Any indirect or direct system call might be intercepted, logged, or blocked by the EDR, making stealth operations and legitimate debugging more difficult.
The Solution: Unhooking
To get around these user-mode hooks, one common technique is unhooking. This usually involves:
- Loading a clean copy of ntdll.dll from disk (not the possibly hooked one in memory).
- Extracting the .text section from the clean copy.
- Overwriting the .text section in memory with the clean one.
This effectively restores the original system call stubs (mov r10, rcx; mov eax, syscall_number; syscall) and removes the user-mode redirection set up by EDR.