About
I’m always curious, experimenting, and seeking ways to turn ideas into real, working solutions.
My Projects
Check out some of my Projects. Cybersecurity and full-stack developer who loves building secure web apps, solving CTF challenges, and sharing knowledge through blogs and projects.
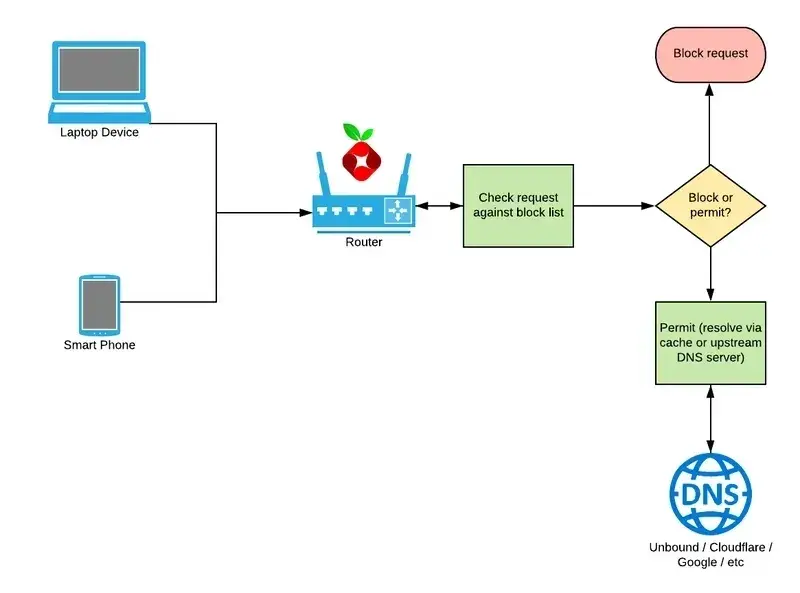
Ad Blocker
A lightweight DNS-based ad blocker written in C++ that intercepts and filters unwanted domains at the network level.
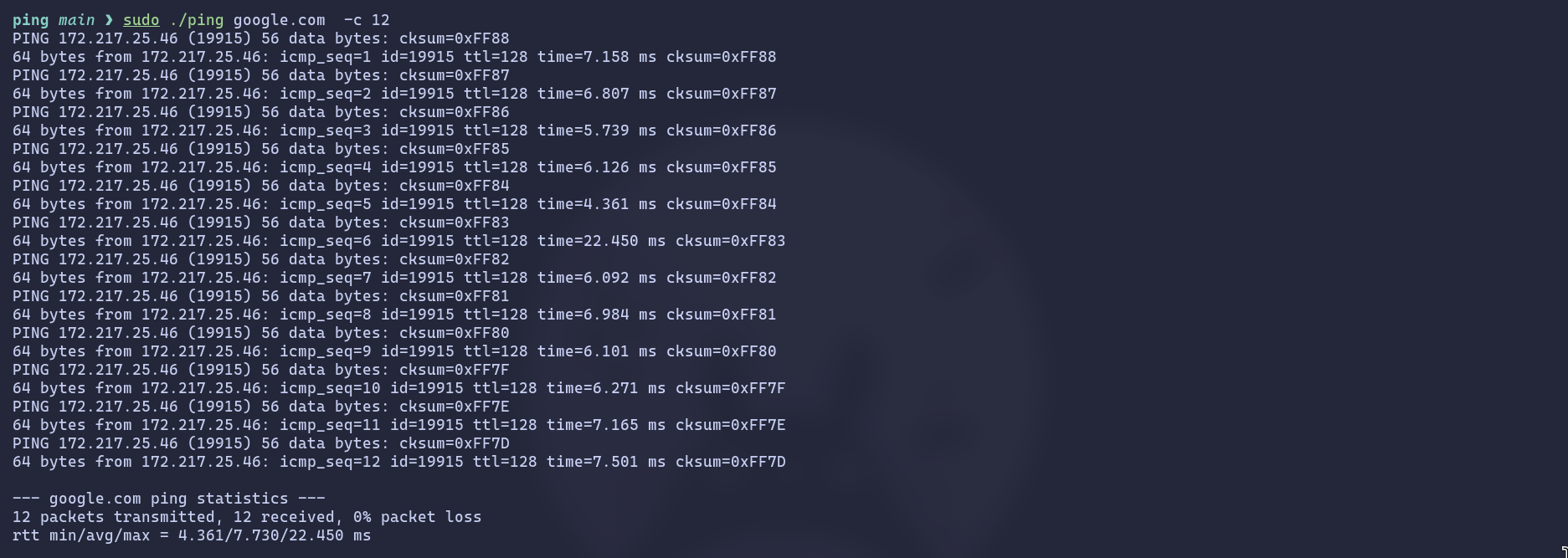
Ping
A C++ raw ICMP ping utility that sends ICMP Echo Requests to a host, measures round-trip time, and prints results. Uses threads to receive replies, calculates checksums, handles timeouts, and shows statistics including min/avg/max RTT and packet loss. Supports -c for count.
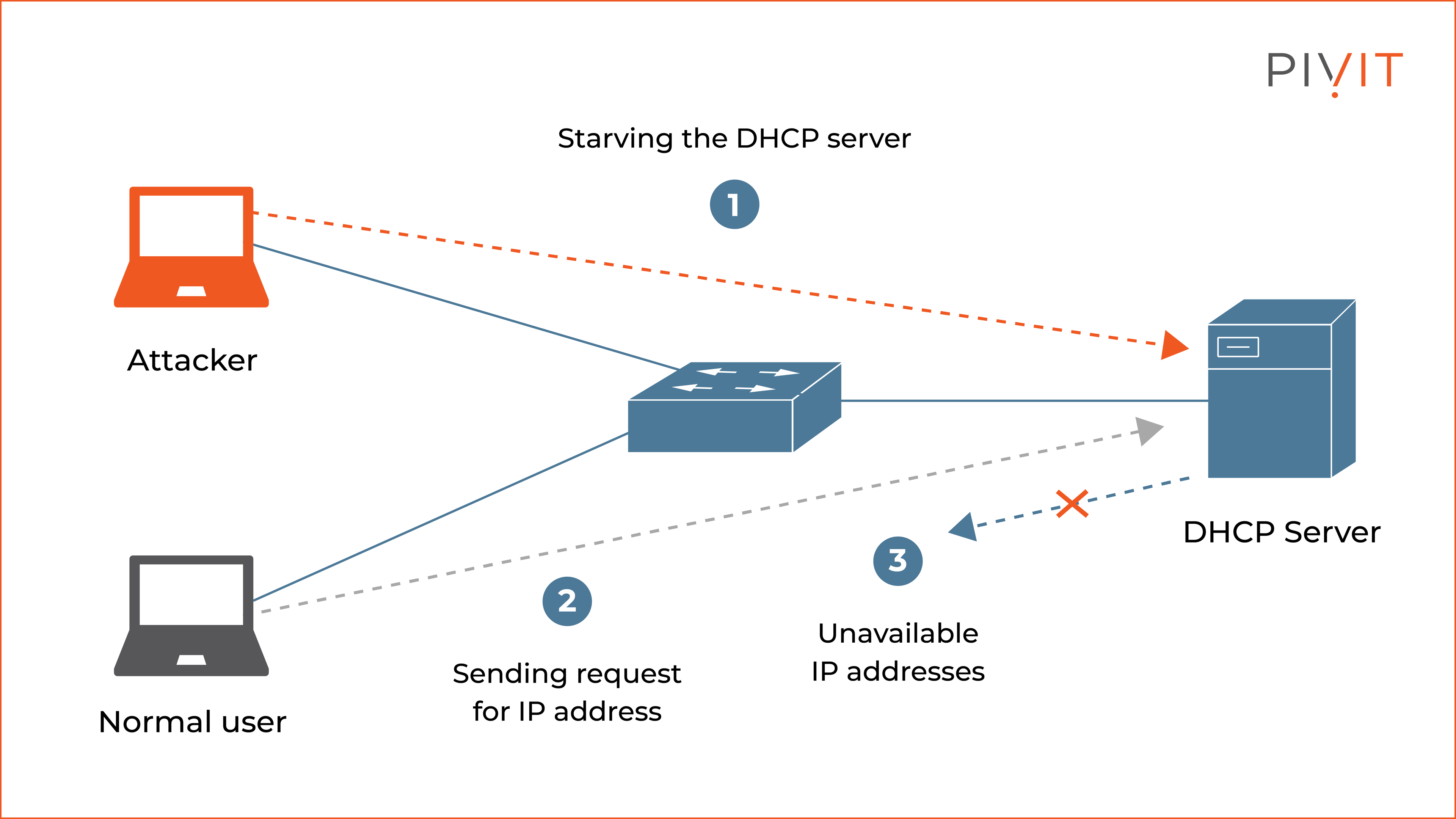
DHCP spoofer
A network attack tool for performing man-in-the-middle attacks using DHCP spoofing.
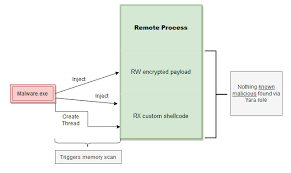
Process remote injection
Remote Process Injection via Thread Hijacking with Dynamic API Resolution and Hashing-Based Stealth Execution
Go HTTP server
A fully custom HTTP server implemented in Go, supporting request parsing, partial parsing, static file serving, and dynamic endpoint handling.
My latest Blogs
I write about cybersecurity, programming, and problem-solving from building secure full-stack applications to breaking down CTF challenges and practical guides for developers. My goal is to share insights that help others learn, build, and stay ahead in tech. .

HTB Cap: Pcap Analysis, Credential Leak, Privilege Escalation
Cap targets IDOR and Linux Capabilities. Exploiting a URL parameter leak on the dashboard reveals a PCAP with FTP credentials for user nathan. After SSH access, we abuse the cap_setuid privilege on Python 3.8 to manipulate the UID to 0 and spawn a root shell.
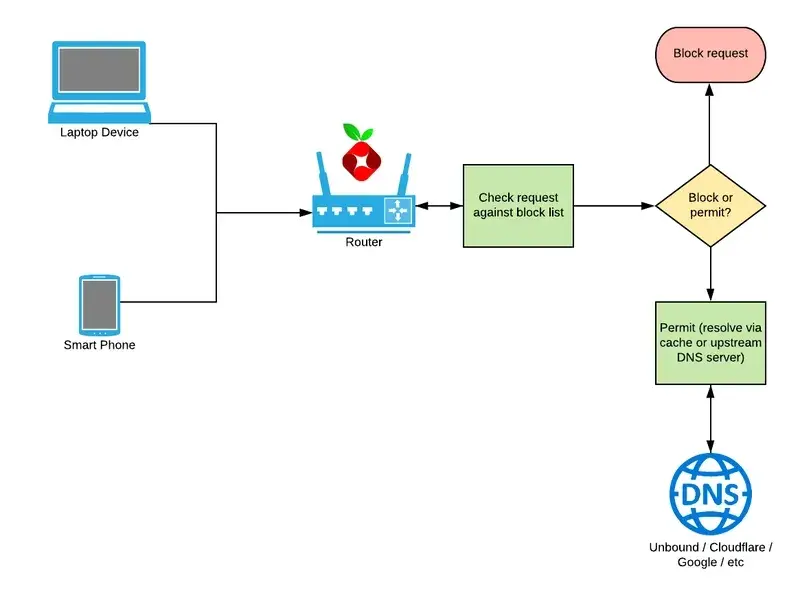
Ad Blocker
A lightweight DNS-based ad blocker built in C++ that intercepts unwanted domains at the network level, no browser extensions needed. Fast, low-level, and efficient.
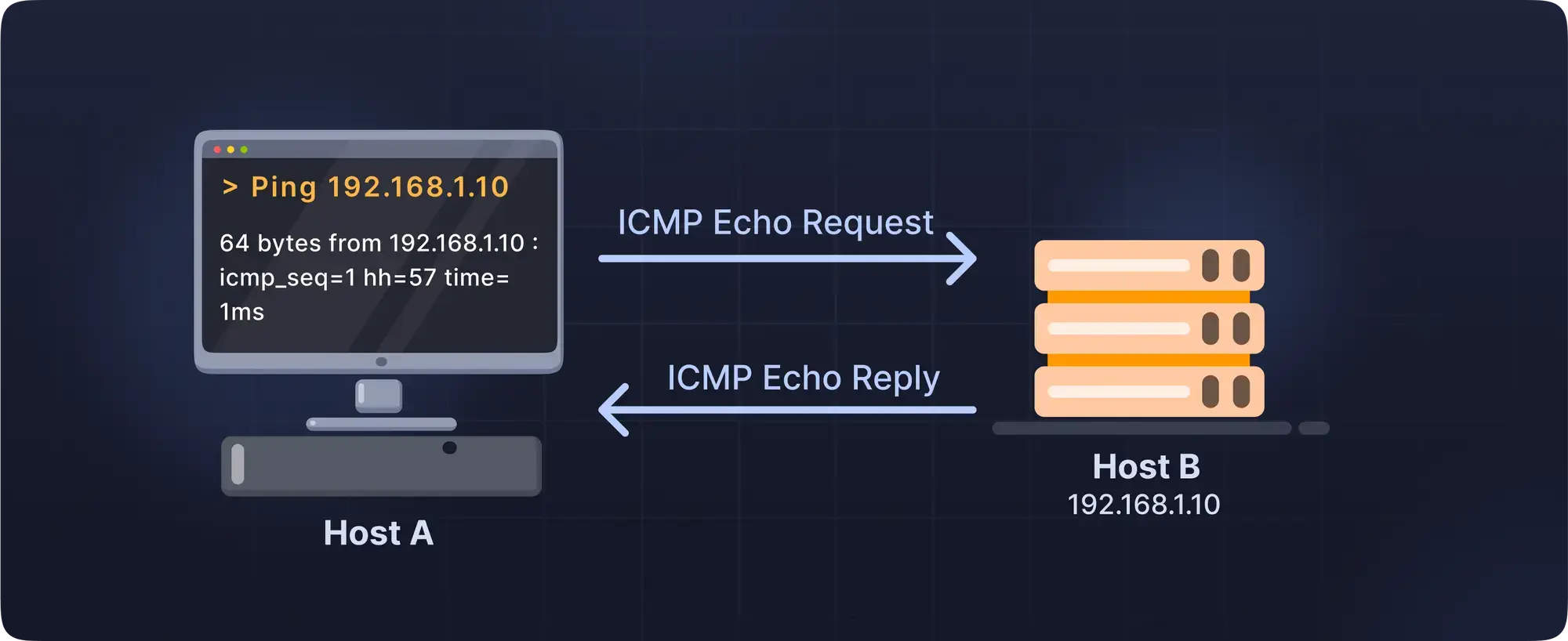
How Ping work?
A C++ raw ICMP ping utility that sends ICMP Echo Requests to a host, measures round-trip time, and prints results. Uses threads to receive replies, calculates checksums, handles timeouts, and shows statistics including min/avg/max RTT and packet loss. Supports -c for count.

TombWatcher
TombWatcher, a complex Active Directory machine. This walkthrough covers Kerberoasting, abusing Group Managed Service Accounts (gMSA), and escalating privileges through a creative ADCS ESC15 certificate vulnerability. A multi-stage attack from user to full domain compromise.

Certificate.htb
From a null-byte upload to SYSTEM. Pivoted through users by abusing ADCS, then leveraged SeManageVolume and SeImpersonate privileges to dump the final admin hash.